Understanding the Science Behind Wireless Technology: How It Connects Us
Understanding the Science Behind Wireless Technology begins with the fundamental principles of electromagnetic waves. These waves allow information to be transmitted over distances without physical connections, connecting devices seamlessly. Wireless technology leverages this phenomenon, utilizing various frequencies across the electromagnetic spectrum, such as radio waves, microwaves, and infrared. Each of these frequency bands carries different data rates and distances, bridging the gap between devices such as smartphones, laptops, and IoT gadgets. The rapid growth of wireless communication technologies, including Wi-Fi and cellular networks, has transformed how we interact with the digital world, making information accessible anytime, anywhere.
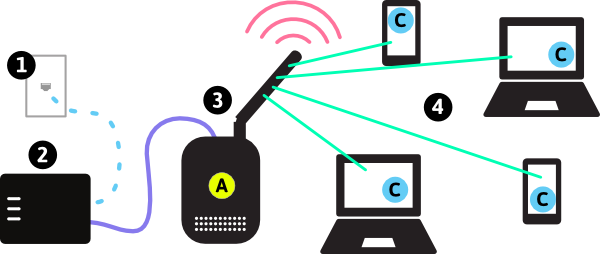
At the core of wireless technology are several critical components: antennas, transmitters, and receivers. Antennas convert electrical signals into electromagnetic waves and vice versa. Transmitters encode information into these waves, while receivers decode the information for devices to understand. Additionally, protocols like Bluetooth and Wi-Fi dictate how devices communicate, ensuring seamless connectivity and data exchange. With advancements in wireless network technology, such as the rollout of 5G, the speed and efficiency of wireless connections are set to improve even further, enhancing our connected experiences in everyday life.
Counter-Strike is a popular online multiplayer first-person shooter game that has captivated players around the world since its initial release. With its strategic gameplay, team-based mechanics, and intense competitive matches, it has become a staple in the esports community. Many gamers also seek out equipment that enhances their experience, such as Top 10 Android Phone Accessories to improve their gameplay and overall enjoyment.
The Future of Wireless Communication: What Innovations to Expect
The future of wireless communication is poised for transformative innovations that promise to redefine how we connect and interact with technology. One of the most anticipated advancements is the rollout of 5G technology, which offers unparalleled speeds and reduced latency, enabling real-time communication for emerging technologies like virtual reality (VR) and the Internet of Things (IoT). In addition, 6G, though still in its conceptual stages, is expected to push boundaries even further, with projections of speeds reaching up to 100 times faster than 5G. This leap in technology could facilitate advancements in smart cities, autonomous vehicles, and advanced telemedicine.
Moreover, as we look to the horizon, several key innovations are set to revolutionize wireless communication. These include:
- Massive MIMO (Multiple Input Multiple Output) technology, which enhances capacity and efficiency by utilizing multiple antennas.
- Beamforming, a technique that focuses signals towards specific users, reducing interference and improving user experience.
- Satellite Internet, which aims to provide global coverage, especially for remote and underserved areas, will change the accessibility landscape.
Wireless Security: How Safe Are Our Connections?
The prevalence of wireless networks in our daily lives has revolutionized the way we connect and communicate. However, with the convenience of wireless security comes the question: how safe are our connections? Many users underestimate the threats posed by unsecured networks, primarily due to a lack of knowledge. According to a recent study, nearly 60% of individuals do not change default passwords on their routers, leaving them vulnerable to unauthorized access. Ensuring robust wireless security requires more than just a simple password; it necessitates a multifaceted approach that includes encryption standards, firewalls, and regular updates to network firmware.
To bolster wireless security, consider implementing the following best practices:
- Utilize WPA3 encryption whenever possible.
- Change default usernames and passwords for your routers and access points.
- Regularly update your network devices to fix vulnerabilities.
- Employ a strong, unique password that combines letters, numbers, and special characters.
- Disable remote management features unless absolutely necessary.